BASHLITE Malware Uses ShellShock to Hijack Devices Running BusyBox - SecurityWeek
Por um escritor misterioso
Descrição
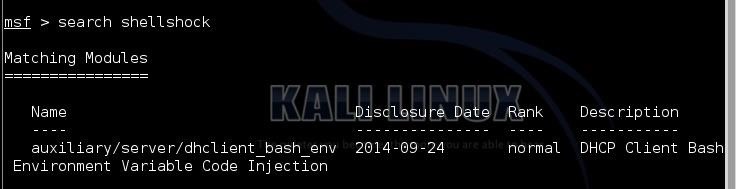
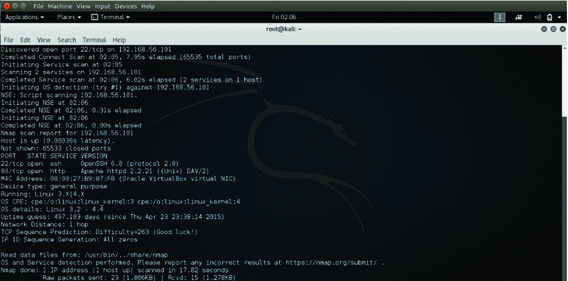
Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null Byte :: WonderHowTo

PDF) IOT Malware : An Analysis of IOT Device Hijacking

Bashlite Updated with Mining and Backdoor Commands
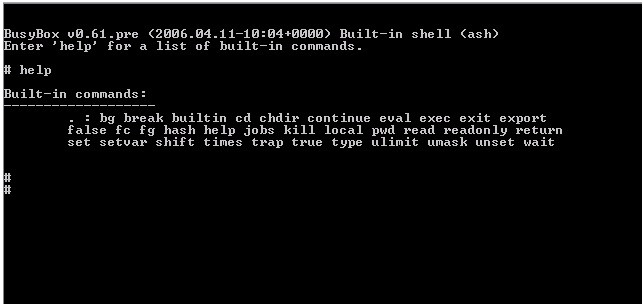
BusyBox Devices Compromised Through Shellshock Attack
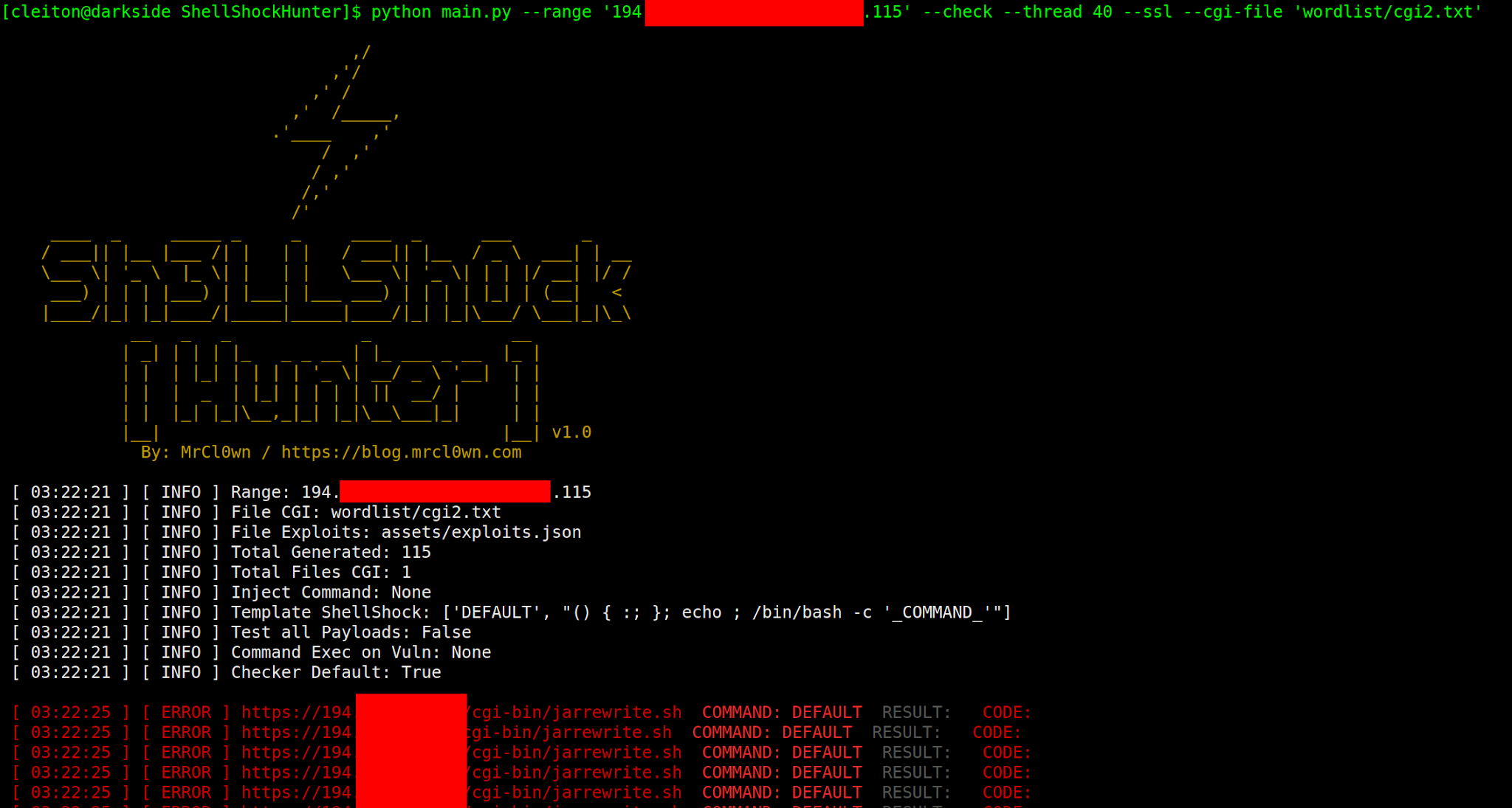
ShellShockHunter - It's A Simple Tool For Test Vulnerability Shellshock

New Stealthy Shikitega Malware Targeting Linux Systems and IoT Devices

Shellshock Attacks in Cyber Security, by Adel the whiteboard security guy 🛡️, Nov, 2023

How to Exploit Shellshock-Vulnerable Websites with Just a Web Browser « Null Byte :: WonderHowTo
BusyBox Devices Compromised Through Shellshock Attack
BASHLITE Malware Uses ShellShock to Hijack Devices Running BusyBox - SecurityWeek

What is Shellshock? This infographic explains how a Shellshock attack works and how to stay safe – Sophos News

Hack The Box - Shocker - David Martinez - Blog
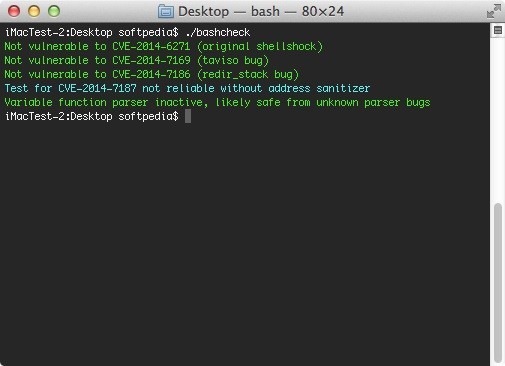
Shellshock Vulnerability Exploitation and Mitigation: A Demonstration
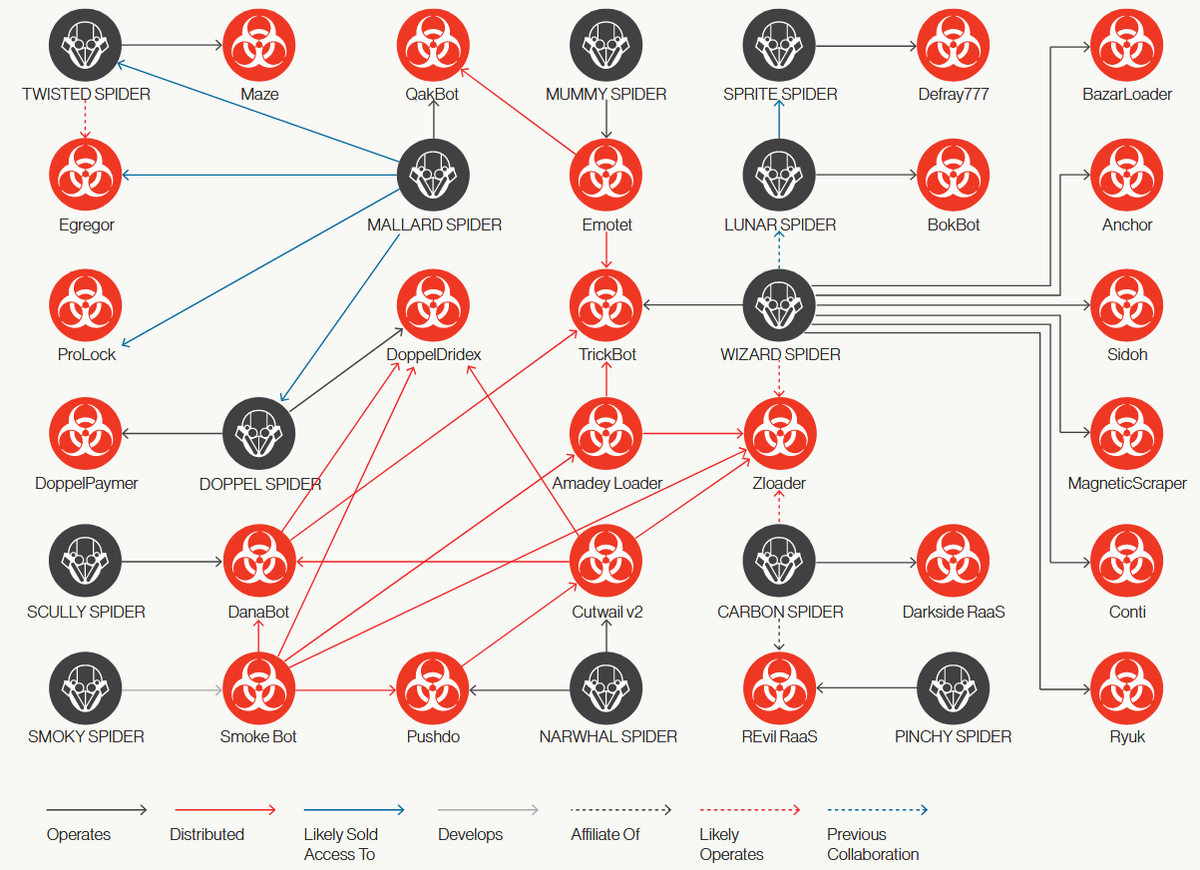
Surge in malware loaders activity: A dangerous trend before the Christmas
de
por adulto (o preço varia de acordo com o tamanho do grupo)