window.open(url, name) is vulnerable to XSS with name collision · Issue #262 · w3c/html · GitHub
Por um escritor misterioso
Descrição
Xiaoran Wang (xiaoran@attacker-domain.com) This is a joint research with Travis Safford. window.open(url, name, [args]) makes it easy for websites accepting user supplied URLs to be vulnerable when attackers can cause a collision on the

Ckan, PDF, File Format

java - Xss Vulnerability - Stack Overflow
Offensive-Payloads/Cross-Site-Scripting-XSS-Payloads.txt at main · InfoSecWarrior/Offensive-Payloads · GitHub

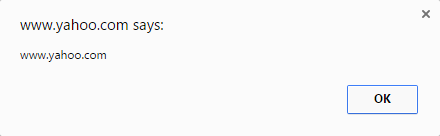
Cross Site Scripting through callback functionality

Add support for inline JS/CSS with #attached [#2391025]

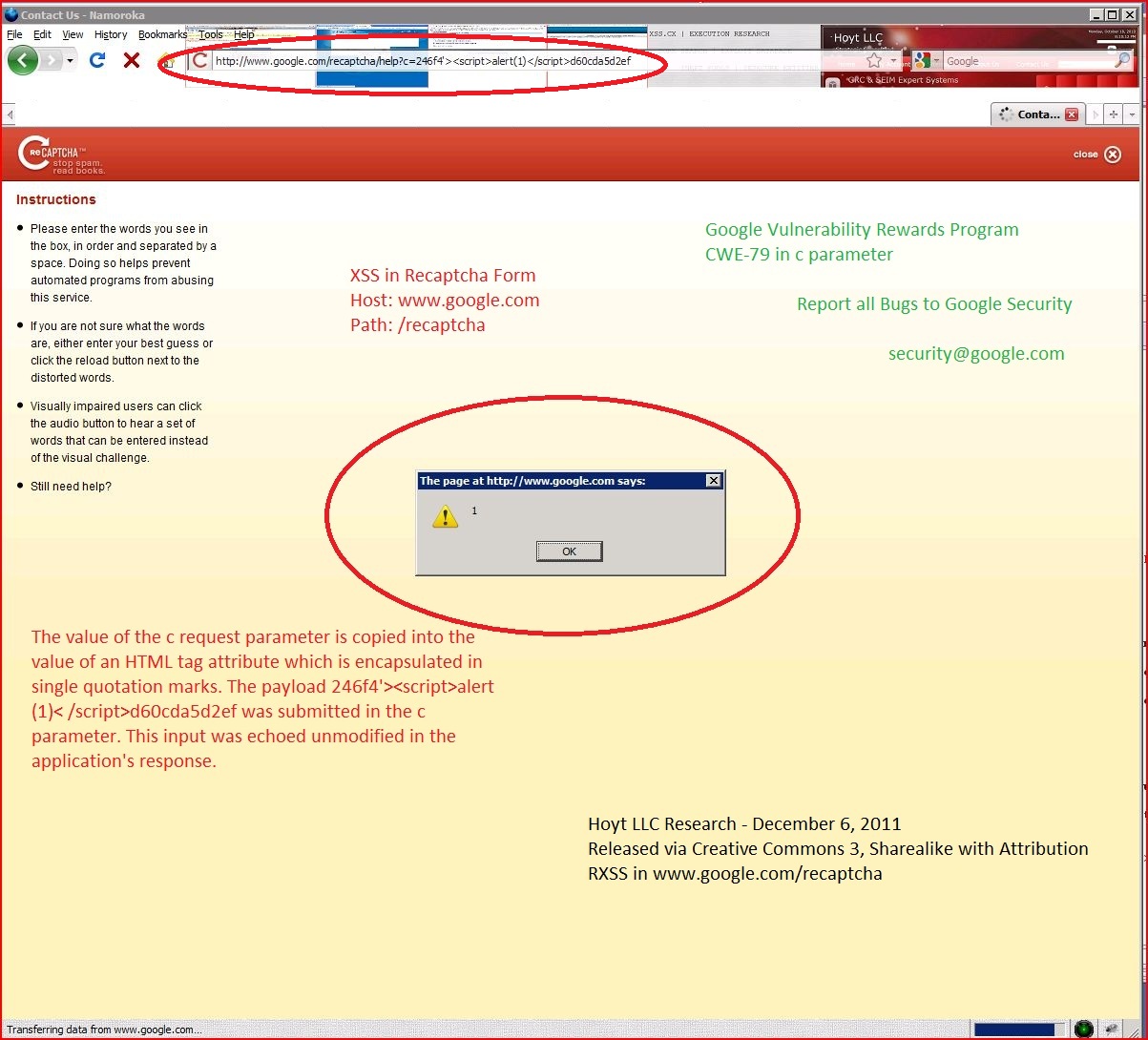
Mutation XSS in Google Search
GitHub - payloadbox/xss-payload-list: 🎯 Cross Site Scripting ( XSS ) Vulnerability Payload List

java - Invalid port. Exiting..Exception in thread main org.openqa.selenium.WebDriverException: Driver server process died prematurely ChromeDriver Selenium - Stack Overflow
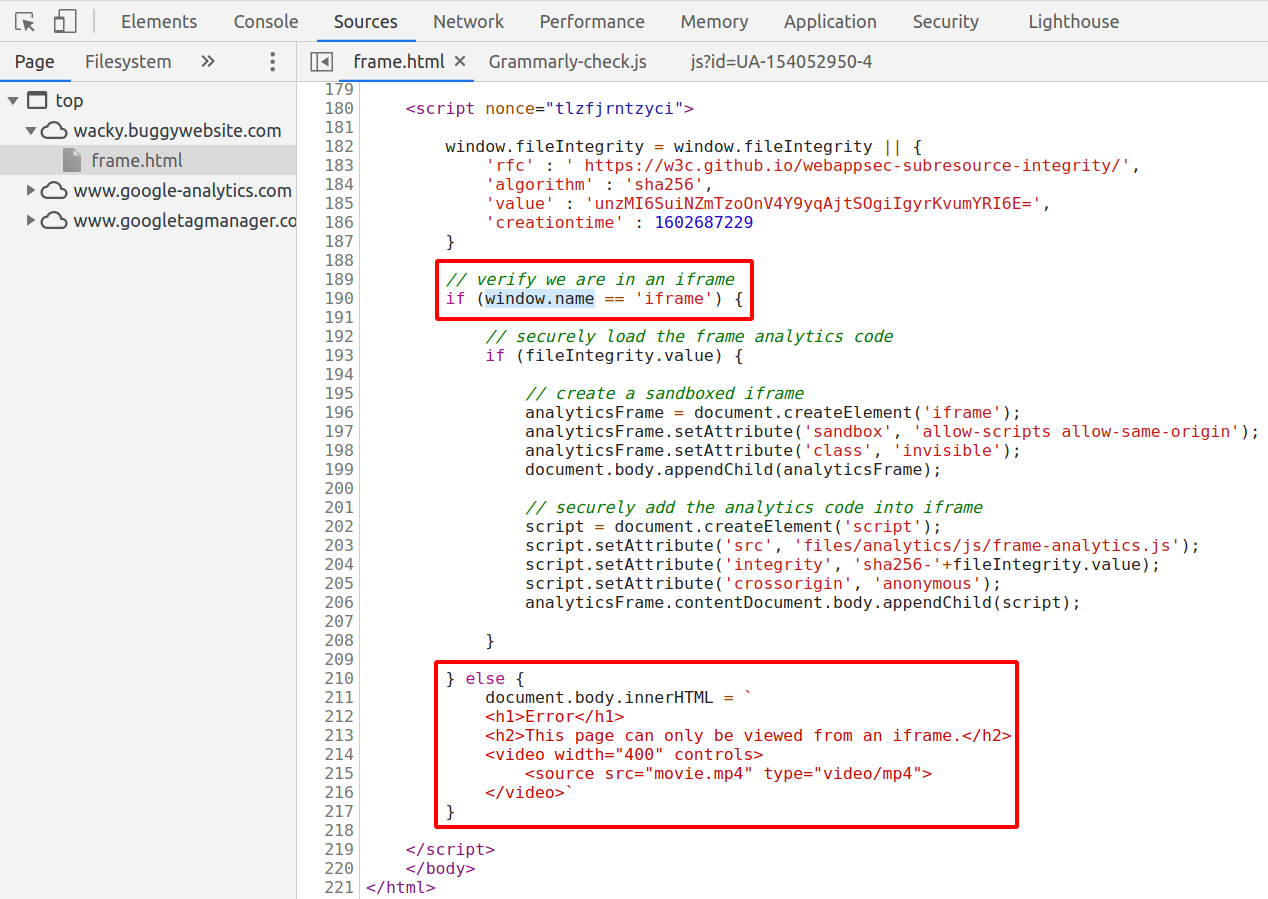
Wacky XSS challenge write-up. On November 4th BugPoc published a new…, by Daniel Santos

Office 365 Hacked Using Google Open-Redirect Vulnerability

Wacky XSS challenge write-up. On November 4th BugPoc published a new…, by Daniel Santos
de
por adulto (o preço varia de acordo com o tamanho do grupo)