SQL injection and XSS: what white hat hackers know about trusting
Por um escritor misterioso
Descrição
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
sql injection, Breaking Cybersecurity News

Input validation errors: The root of all evil in web application security

What is SQL Injection?, Explanation & Protection

Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques

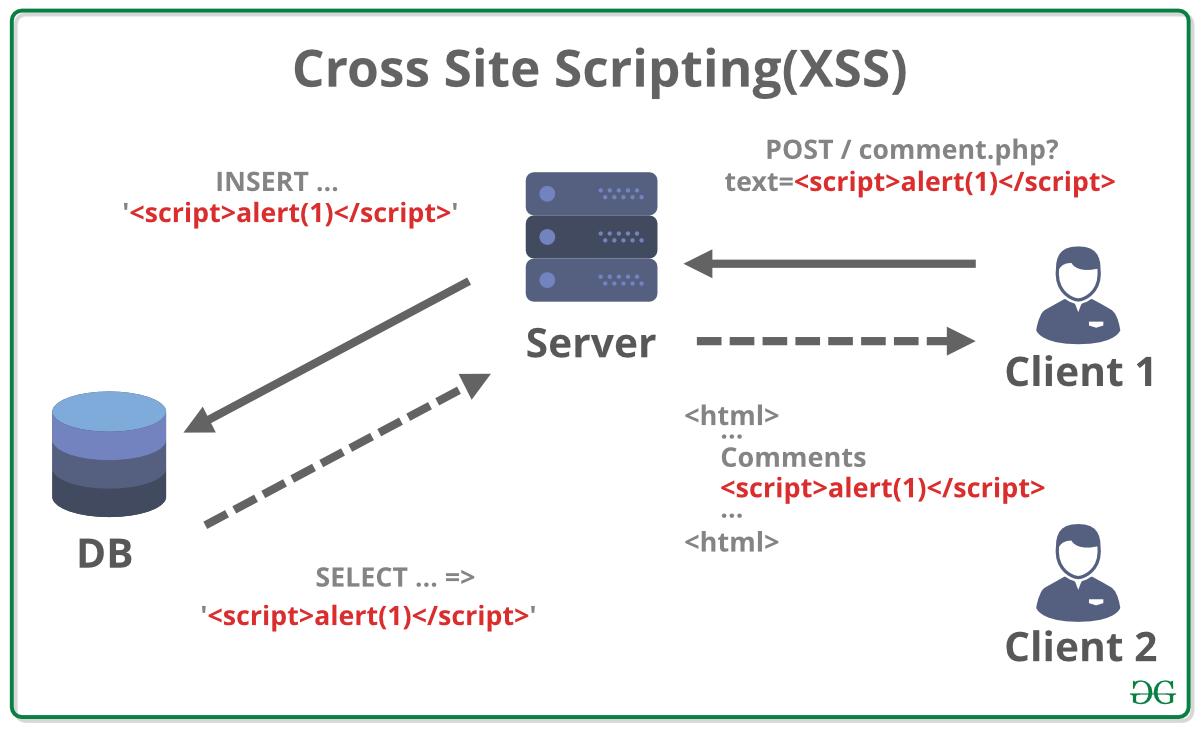
What is Cross-site Scripting and How Can You Fix it?

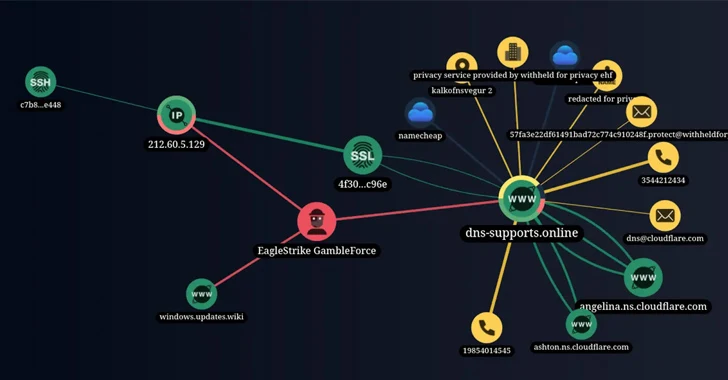
Network Vulnerabilities and Threats

PDF) Web Based XSS and SQL Attacks on Cloud and Mitigation

8 Best Hacking Software for Security Professionals in 2024
PDF) Testing and Comparing Web Vulnerability Scanning Tools for SQL Injection and XSS Attacks

PDF) A Survey on Web Application Vulnerabilities (SQLIA, XSS) Exploitation and Security Engine for SQL Injection

Stealing private data with a CSS injection
5 Phases of ETHICAL HACKING

40+ Best Cross-Site Scripting (XSS) Courses and Certifications for 2023

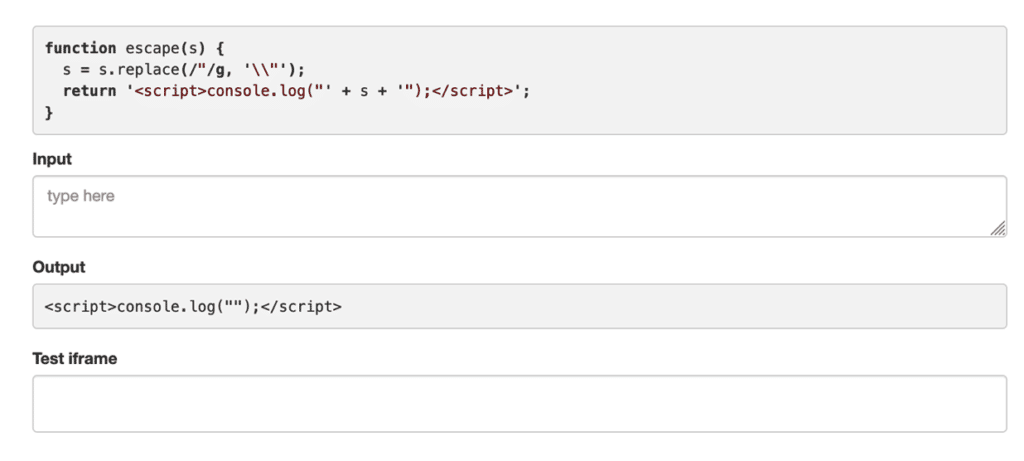
Bug Bytes #10 - Command Injection, Sublert by @yassineaboukir & Bypassing XSS Detection - Intigriti

National Day of Ethical Hacking Special: How to Become an Ethical Hacker?
de
por adulto (o preço varia de acordo com o tamanho do grupo)