NEW BEST Evade SCRIPTS Mobile And Pc, ALL FEATURES
Por um escritor misterioso
Descrição

HTML smuggling: A Stealthier Approach to Deliver Malware - CYFIRMA

Meta Says It Has Busted More Than 400 Login-Stealing Apps This Year
What Is Endpoint Security? Definition, Key Components, and Best Practices - Spiceworks
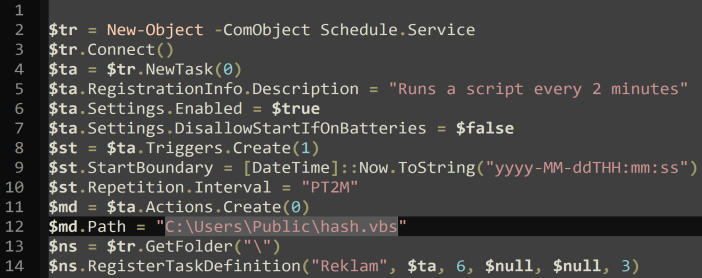
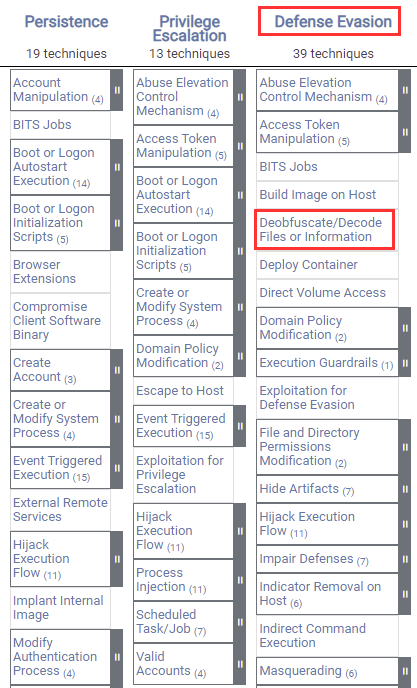
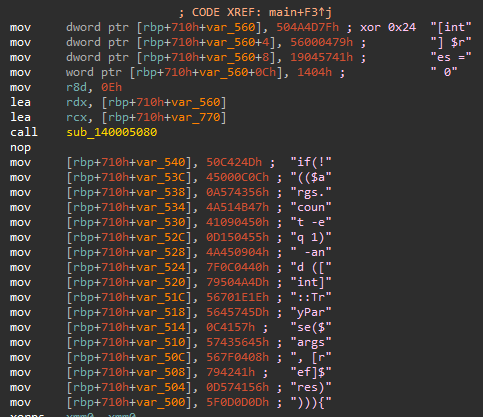
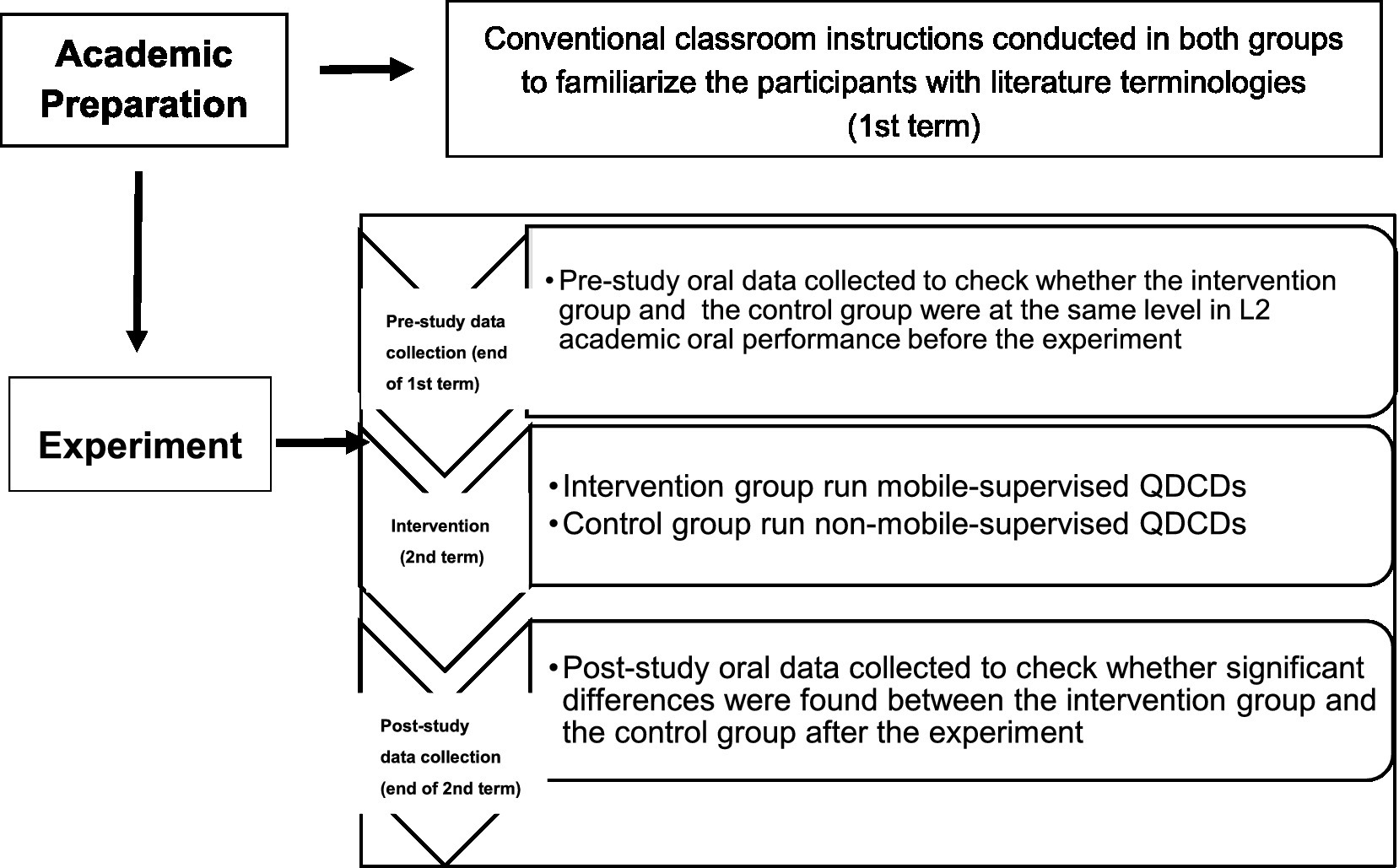
Analyzing AsyncRAT's Code Injection into Aspnet_Compiler.exe Across Multiple Incident Response Cases

Weekly Cybersecurity Briefing - March 29, 2023
Top 10 macOS Malware Discoveries in 2021 A Guide To Prevention & Detection - SentinelOne

Cybersecurity Search Engine
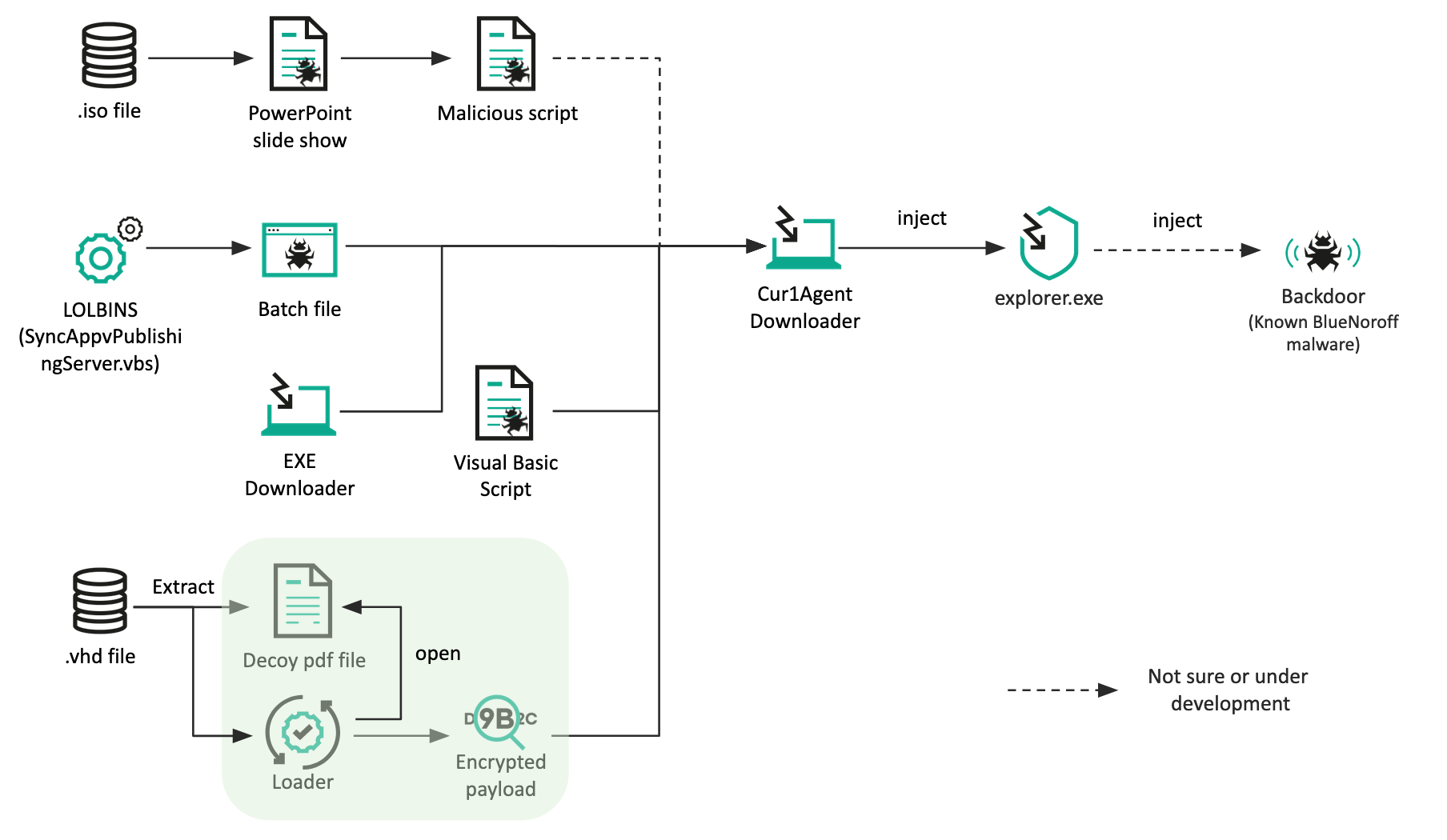
BlueNoroff introduces new methods bypassing MoTW

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

5 Ways To Make Popups Look Great On A Mobile Device (For Your Responsive Website) - Poptin blog

APT33 Hunt Report
Main :: Causality Story Sequencer :: Hollywood Camera Work

Total Defense Premium Internet Security Review

27 Most Notorious Hacks in History that Fall Under OWASP Top 10
de
por adulto (o preço varia de acordo com o tamanho do grupo)