Proxy chaining, ESET Bridge
Por um escritor misterioso
Descrição
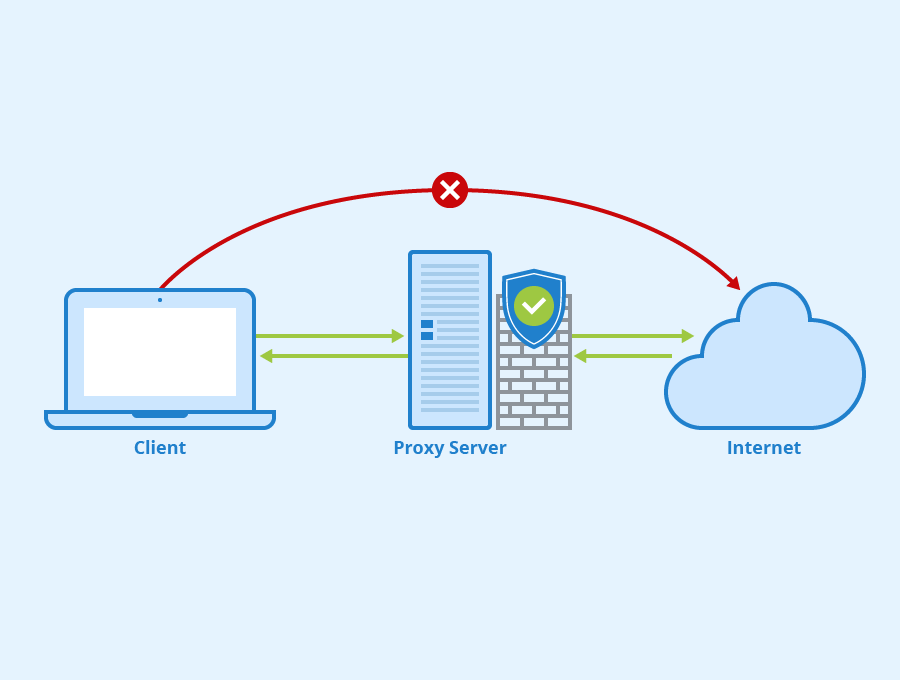
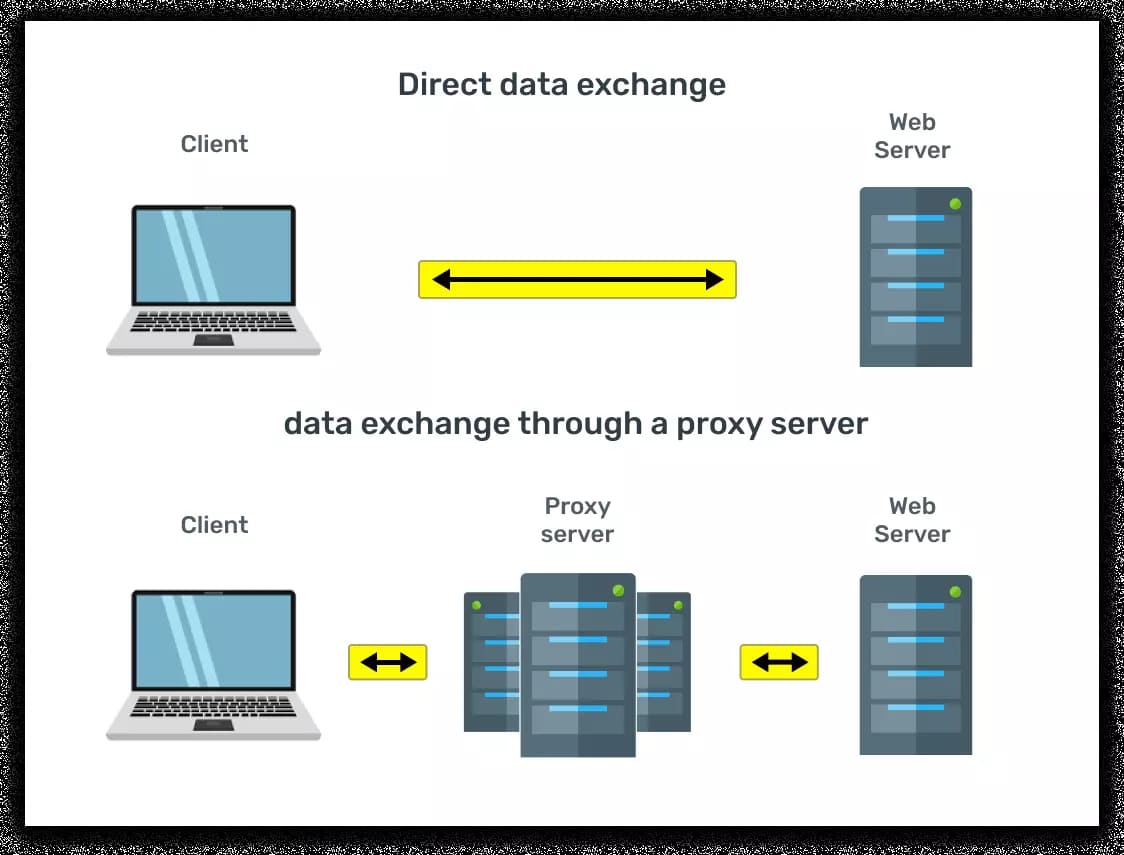
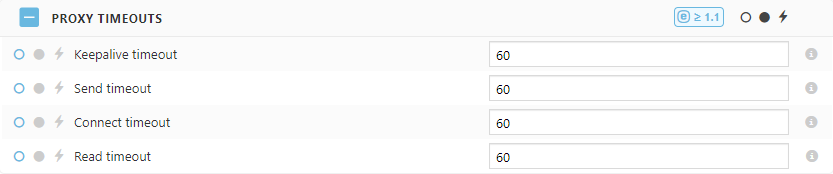
ESET Bridge supports proxy chaining—it can forward the traffic to a remote proxy.

The Anomali Blog

How to install and config ESET Bridge
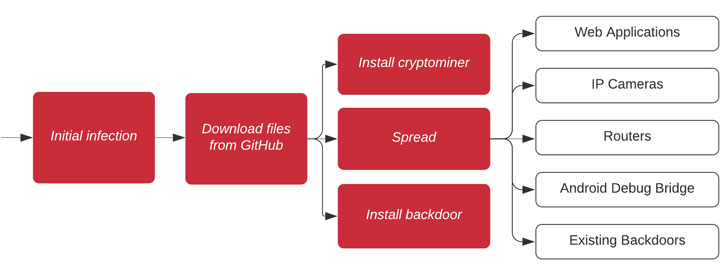
Wormable Gitpaste-12 Botnet Returns to Target Linux Servers, - vulnerability database
KB8368] Advanced scenarios for ESET Bridge with ESET PROTECT On-Prem
Prosecutors Charge Two Men for Roles in Criminal Doxing Group ViLE

802.1X Authentication &Amp; Authorization Deployment For
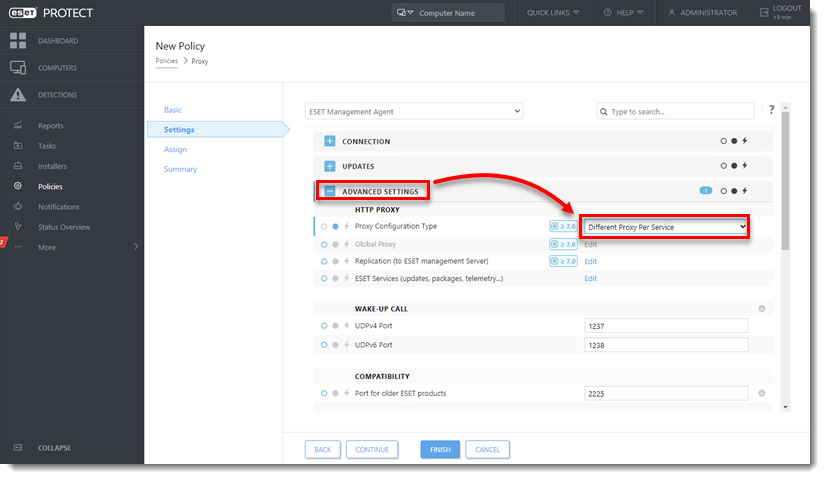
ESET Bridge Policy, ESET Bridge
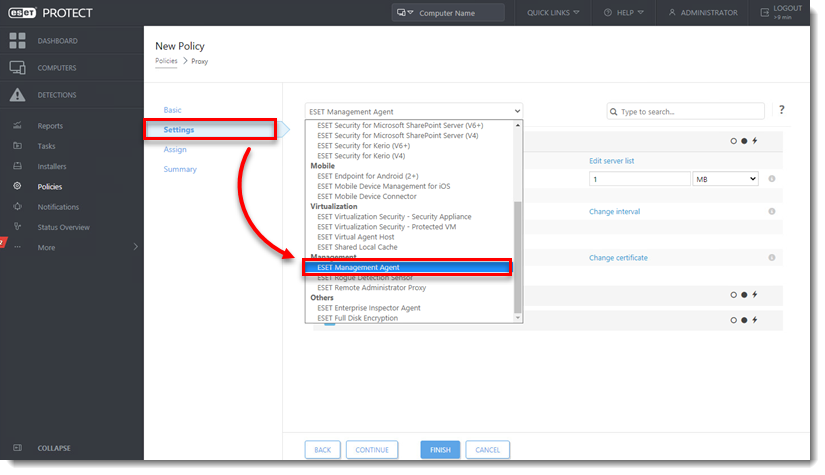
KB8368] Advanced scenarios for ESET Bridge with ESET PROTECT On-Prem

September 2023: Key Threat Actors, Malware and Exploited Vulnerabilities

Lineal Archives - Lineal IT Support - North Devon

The Challenge of Cyber-Attack Technical Attribution in Computer Networks by Stephan Bren - Issuu
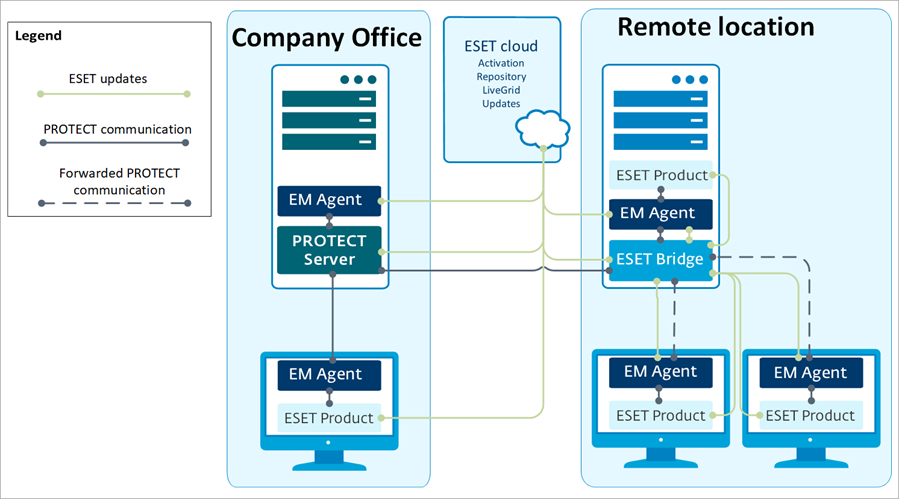
Forwarding of communication between ESET Management Agents and ESET PROTECT Server, ESET Bridge
de
por adulto (o preço varia de acordo com o tamanho do grupo)