Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Top 10 Types of Information Security Threats for IT Teams

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

TryHackMe Hacktivities
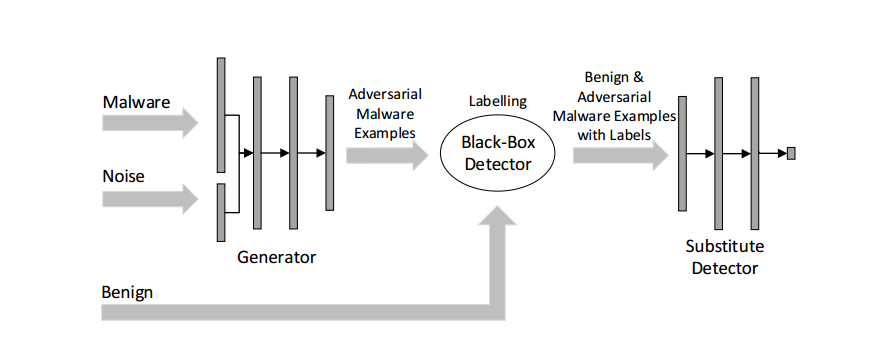
Malware Detection

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Remediation and Malware Detection Overview

Malware Analysis: Steps & Examples - CrowdStrike

Playbook for Malware outbreak

Malware analysis index.html Malicious activity

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Free Cybersecurity Training and Career Development
de
por adulto (o preço varia de acordo com o tamanho do grupo)