Malware analysis Malicious activity
Por um escritor misterioso
Descrição

A detailed analysis of the Menorah malware used by APT34

Malware Analysis Benefits Incident Response

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
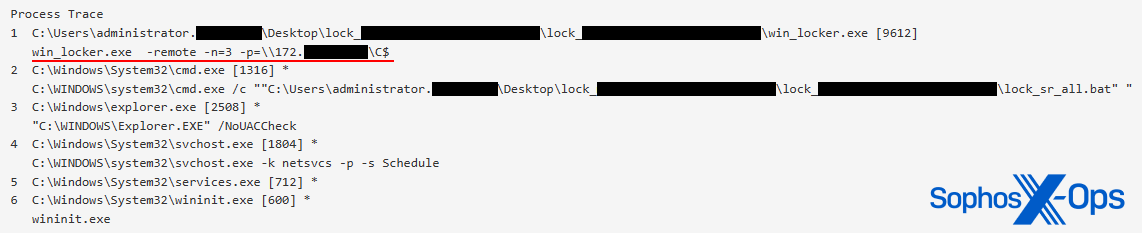
CryptoGuard: An asymmetric approach to the ransomware battle – Sophos News
Most Common Malware Attacks

U.S. law enforcement seizes BlackCat ransomware site, distributes decryption key

How to build a malware analysis sandbox with Elastic Security

Malware Analysis - What is, Benefits & Types (Easily Explained)

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
de
por adulto (o preço varia de acordo com o tamanho do grupo)