Malware analysis Malicious activity
Por um escritor misterioso
Descrição

How to Analyze Malware's Network Traffic in A Sandbox

Malware Analysis: Steps & Examples - CrowdStrike

Unveiling activities of Tropic Trooper 2023 deep analysis of Xiangoop Loader and EntryShell payload

What is Malware? Definition, Types, Prevention - TechTarget

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

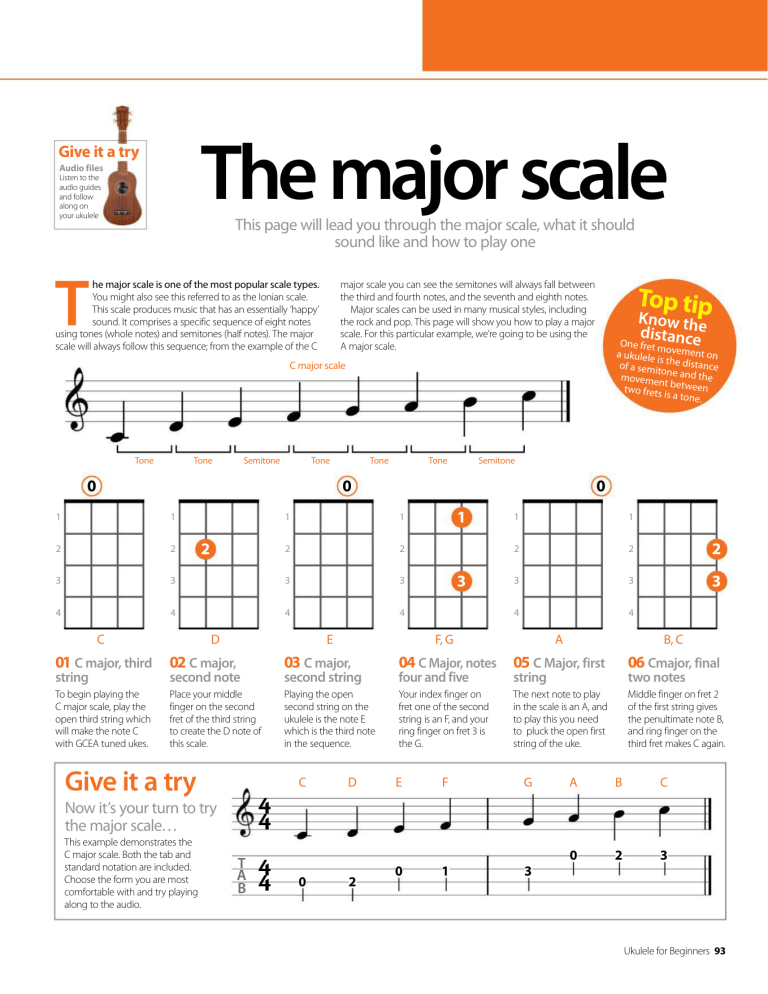
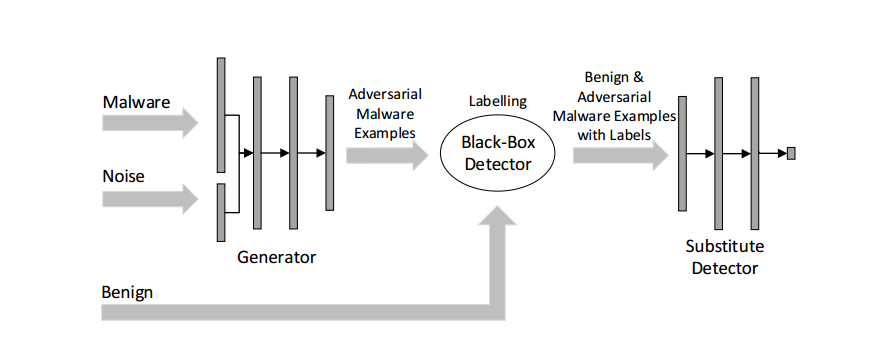
Dynamic malware analysis [34]

Malware Analysis: Protecting Your Network from Cyber Attacks

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Malware Analysis Benefits Incident Response

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware analysis tt.7z Malicious activity
Malware Detection

MetaDefender Cloud Advanced threat prevention and detection
de
por adulto (o preço varia de acordo com o tamanho do grupo)