How can an attacker execute malware through a script? 2022
Por um escritor misterioso
Descrição

Exploring Prompt Injection Attacks, NCC Group Research Blog

What is Malware? Examples & Prevention Tips
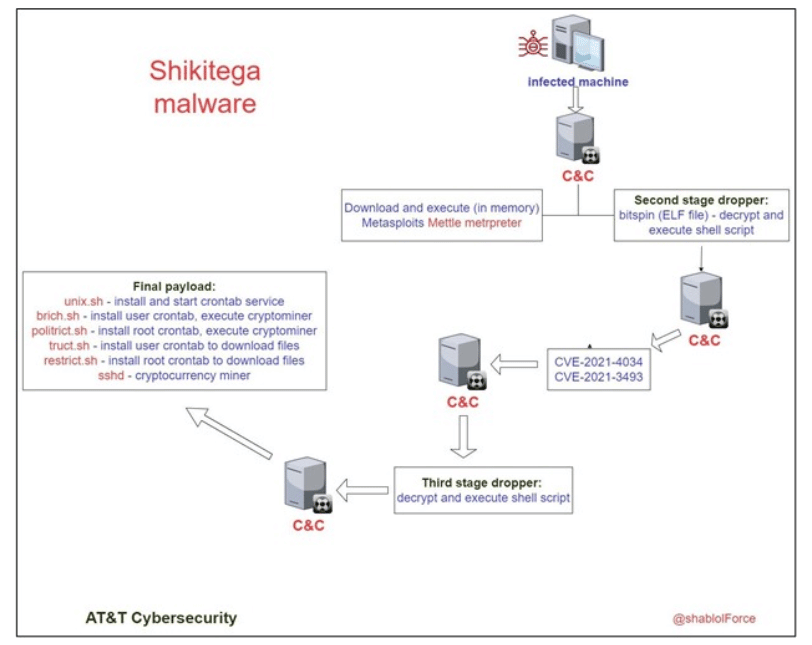
New Linux Malware Shikitega Can Take Full Control of Devices
Top 11 exploited vulnerabilities for initial access and compromise in '22, by Winter_Soldiers

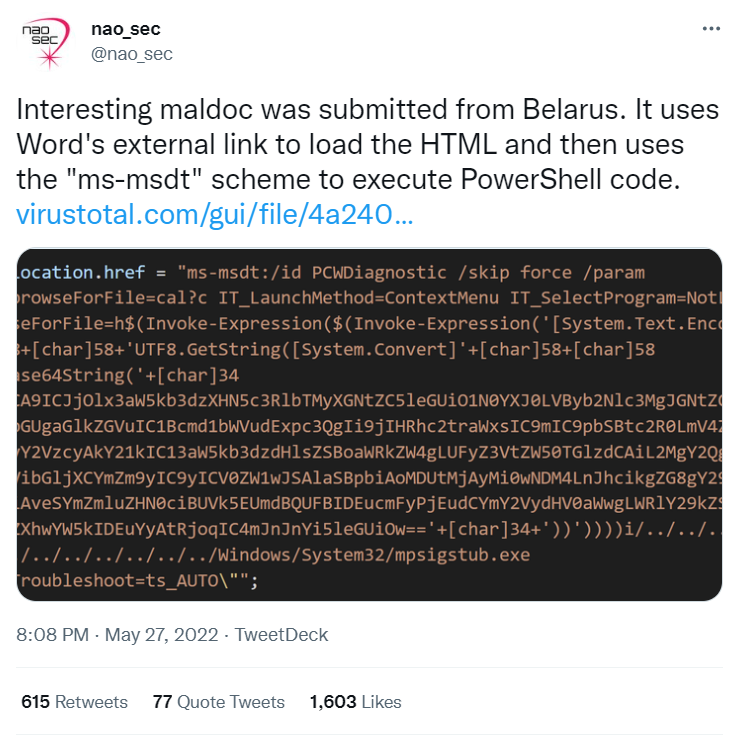
APT28 attack uses old PowerPoint trick to download malware

How Do Hackers Execute Malware Attacks With a Script?
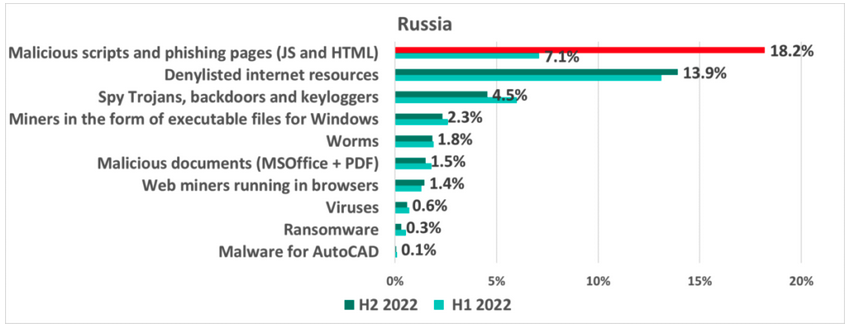
Exploitation of Bitrix CMS Vulnerability Drives ICS Attack Surge in Russia - SecurityWeek
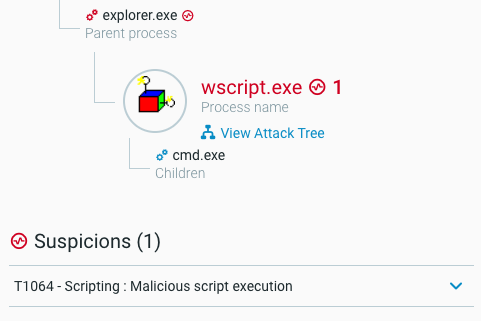
THREAT ANALYSIS REPORT: SocGholish and Zloader – From Fake Updates and Installers to Owning Your Systems
Hunting for Malicious PowerShell using Script Block Logging
de
por adulto (o preço varia de acordo com o tamanho do grupo)
_new-roblox-evade-script-hack-gui-124-auto-farm-124-god-mode-124-infinite-money-amp-more-pastebin-2022-preview-hqdefault.jpg)