Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace
Por um escritor misterioso
Descrição
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.

Xcode png images
Adobe InDesign CS6 Products Programming Guide Volume 2
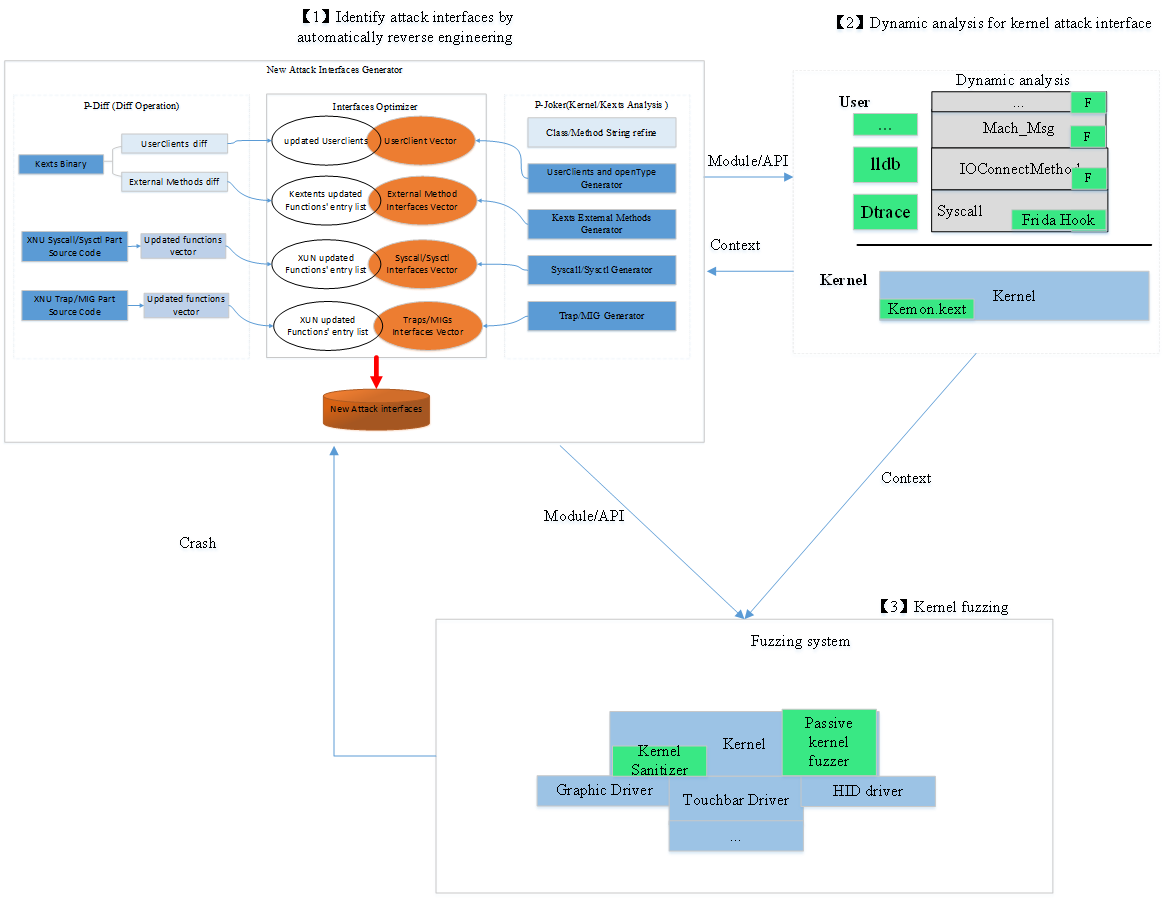
Virus Bulletin :: VB2019 paper: Play fuzzing machine – hunting iOS/macOS kernel vulnerabilities automatically and smartly

CONFidence 2015: DTrace + OSX = Fun - Andrzej Dyjak

Advanced Apple Debugging & Reverse Engineering, Chapter 30: Intermediate DTrace

Advanced Apple Debugging & Reverse Engineering
Reverse Engineering x64 for Beginners - Windows - Checkmate
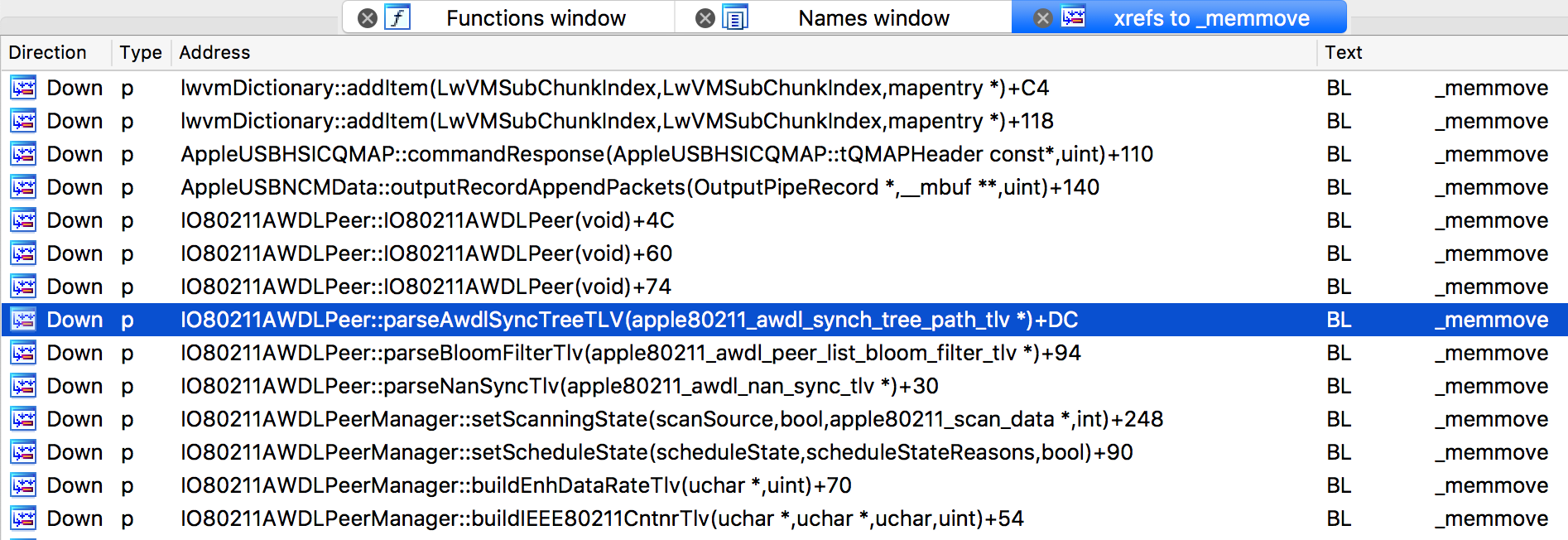
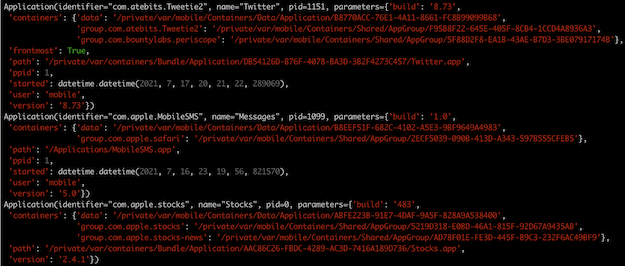
Project Zero: An iOS zero-click radio proximity exploit odyssey

First update to the RxSwift book with version 1.1 // rx_marin

An iOS zero-click radio proximity exploit odyssey - Project Zero
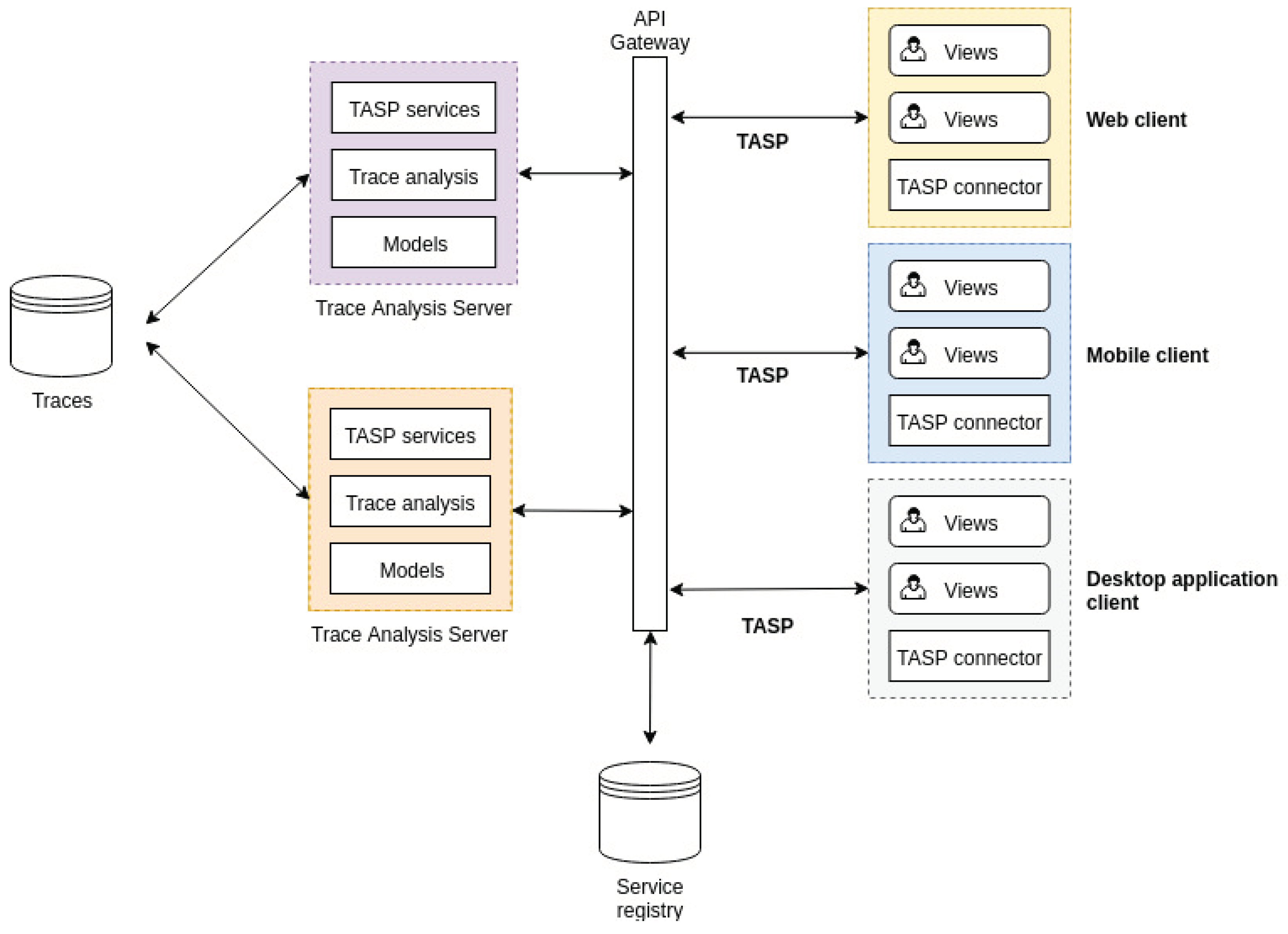
Sensors, Free Full-Text
News Frida • A world-class dynamic instrumentation toolkit

Advanced Apple Debugging & Reverse Engineering, Chapter 30: Intermediate DTrace
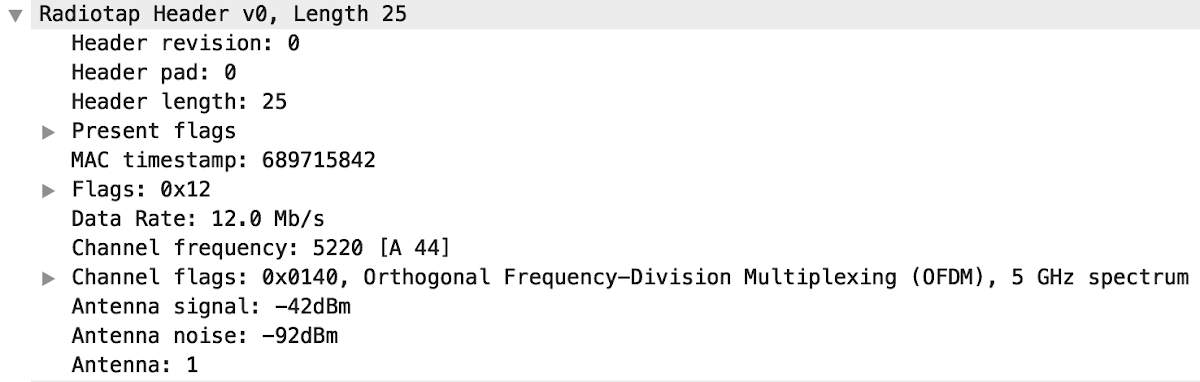
Project Zero: An iOS zero-click radio proximity exploit odyssey
de
por adulto (o preço varia de acordo com o tamanho do grupo)
.jpg)