Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Descrição
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.
Bertrand Meyer's technology+ blog Language design Archives - Bertrand Meyer's technology+ blog

testar – scriptless testing through graphical user interface - Vos - 2021 - Software Testing, Verification and Reliability - Wiley Online Library

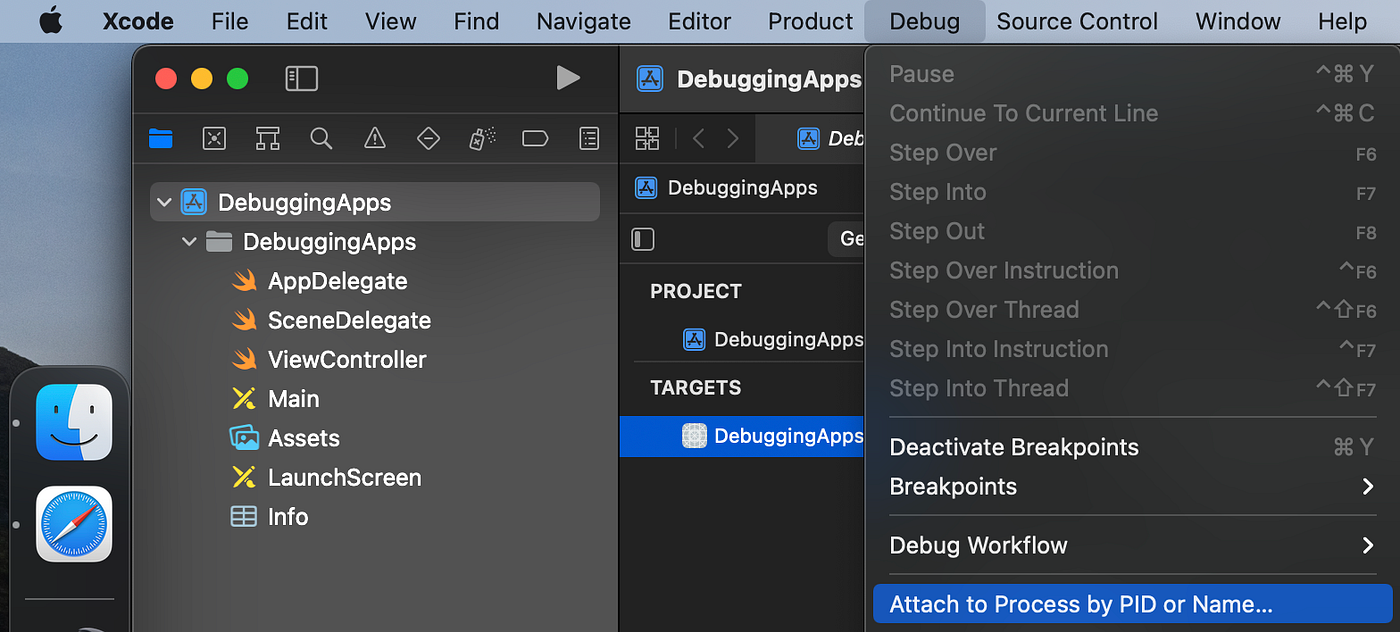
iOS App Reverse Engineering
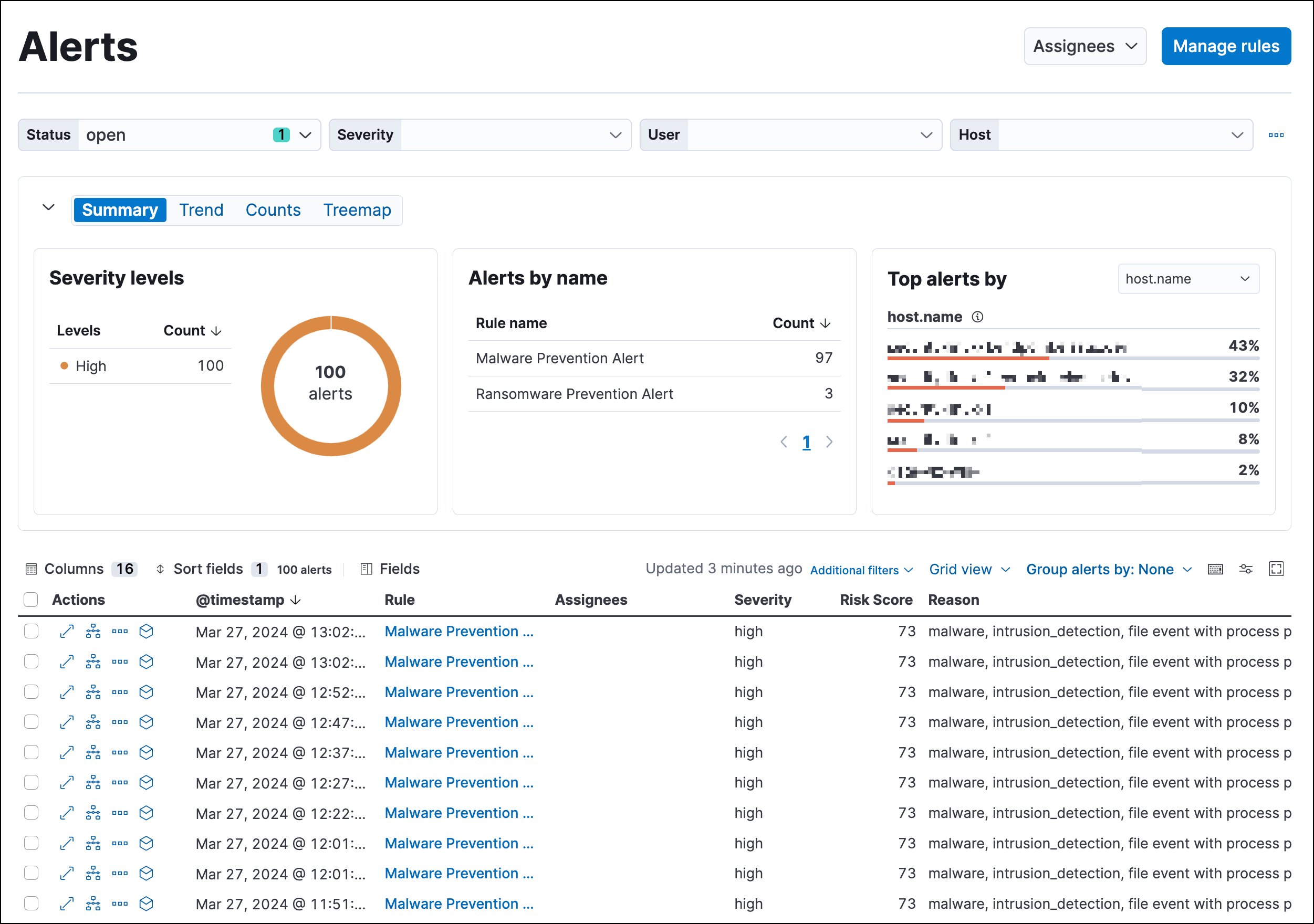
Detections and alerts, Elastic Security Solution [8.11]

Advanced Apple Debugging & Reverse Engineering (3rd Edition) - 2018

LLDB's Runtime Manipulation: A Guide to Advance Debugging and Optimization
iPhone Rootkit? There's an App for that! - Reverse Engineering Mac

2022-2023 College Catalog by Honolulu Community College - Issuu
How to Reverse Engineer an iOS App, by Zafar Ivaev

Teensy Stands In For The Motorola 68k

College Catalog & Student Handbook 2019 - 2020 by Texas State Technical College - Issuu
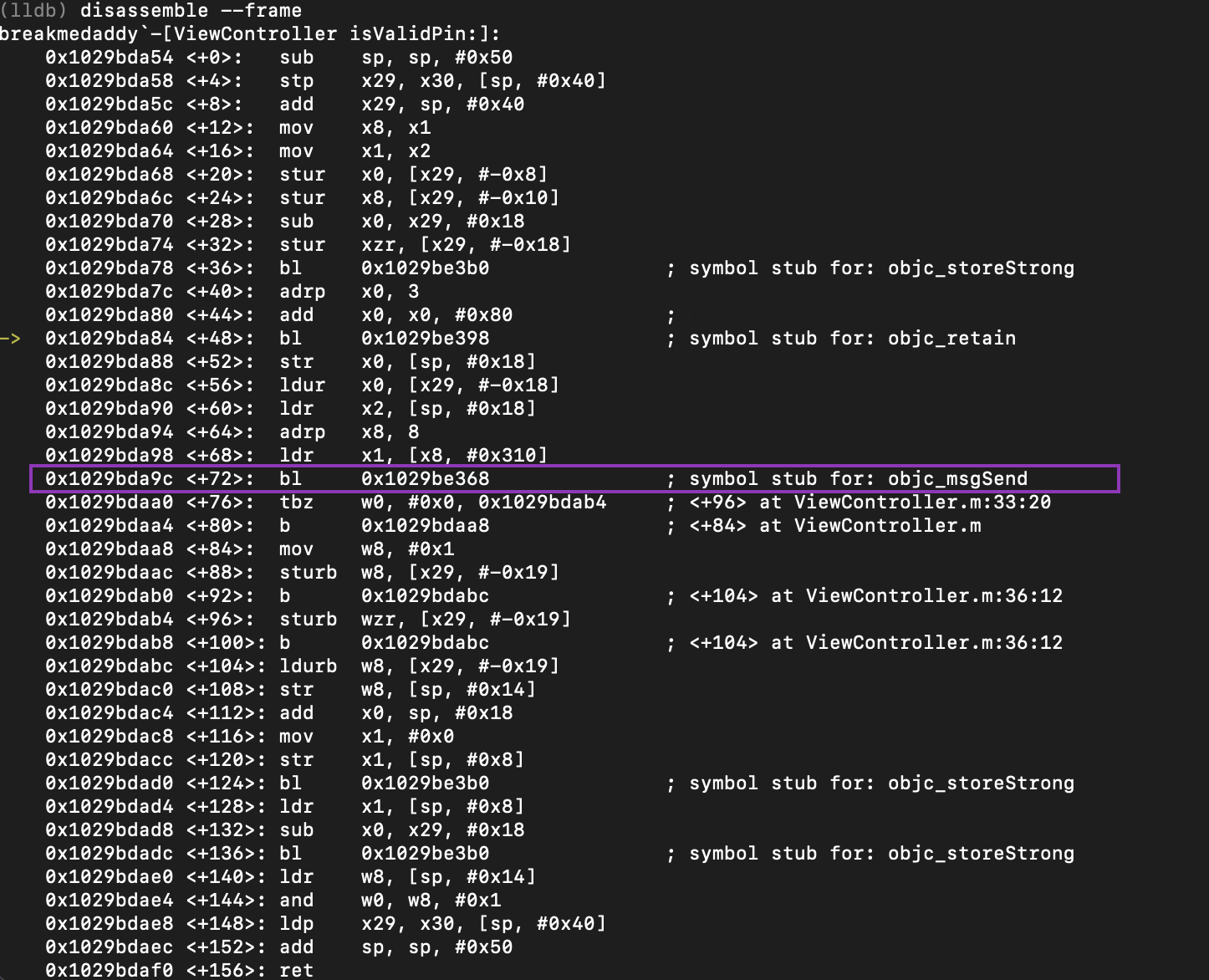
How to Reverse Engineer and Patch an iOS Application for Beginners: Part I
de
por adulto (o preço varia de acordo com o tamanho do grupo)