Credential Stuffing 2.0: The Use of Proxies, CAPTCHA Bypassing
Por um escritor misterioso
Descrição
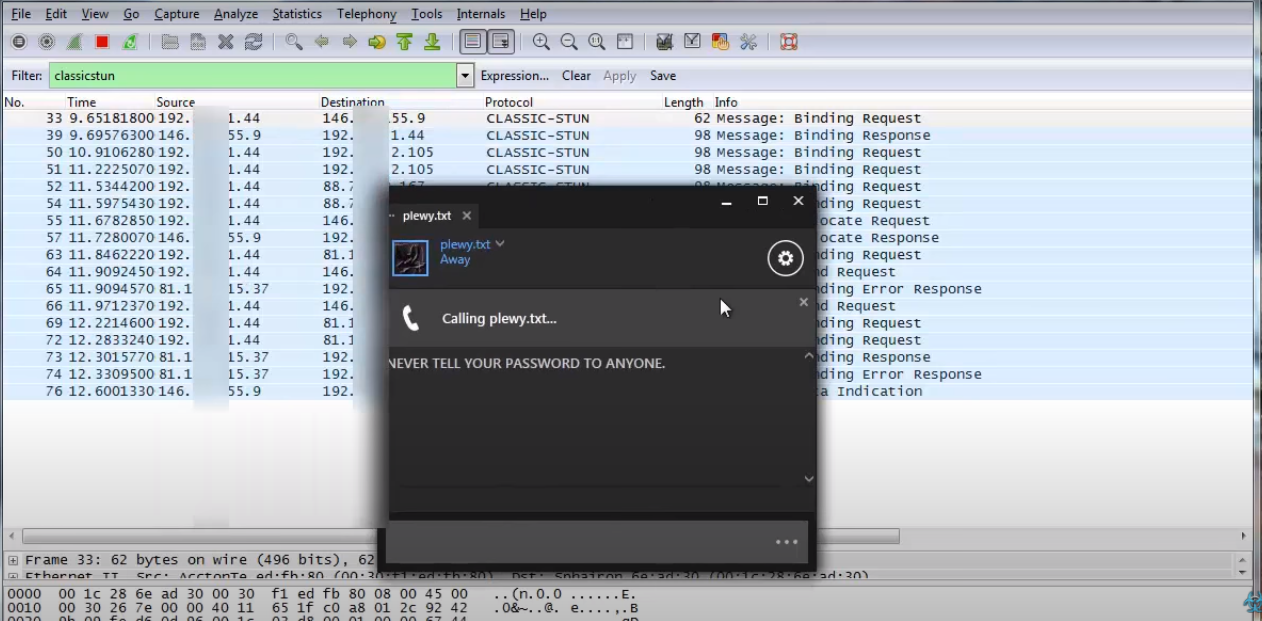
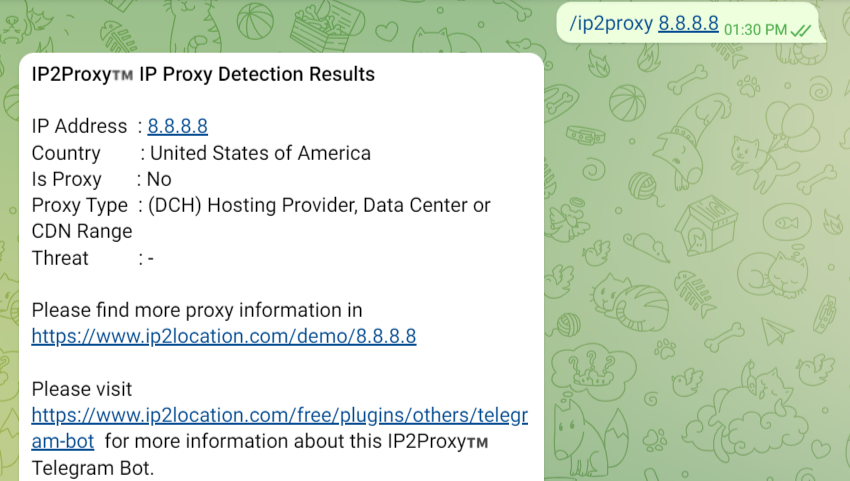
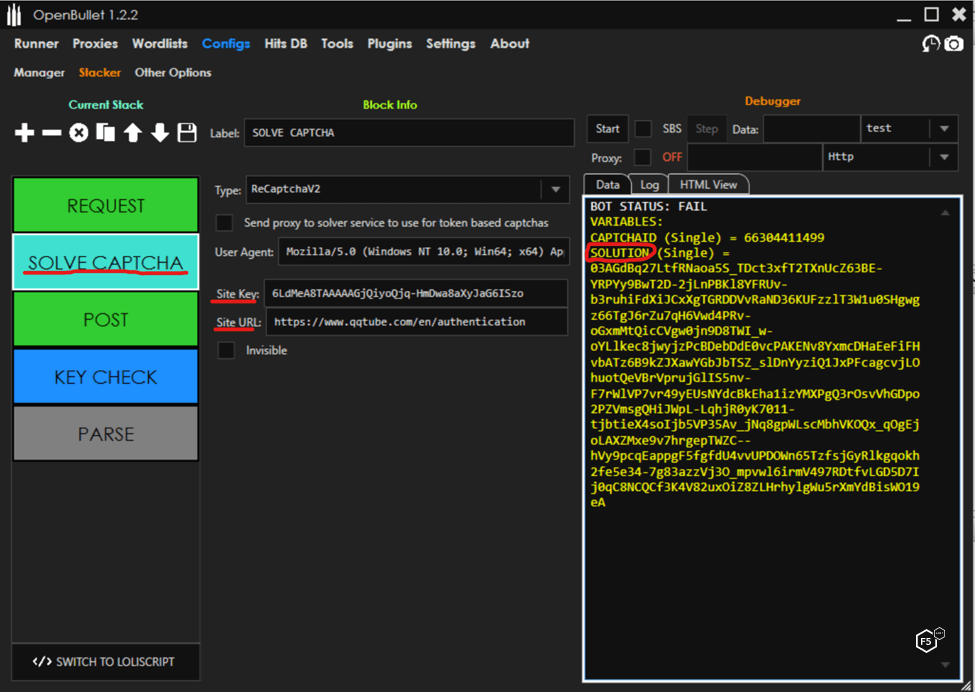
Welcome to the new age of cyber attacks, where hackers have taken credential stuffing to the next level. Meet Credential Stuffing 2.0, where the use of proxies, CAPTCHA bypassing, CloudFlare security, and GUI tools have become the norm..

Skiplagging, CAPTCHA vs Bots, Scraper Bots

10 Tips To Stop Credential Stuffing Attacks, by Jarrod Overson
Email Compromise with Credential Stuffing Attack Tools

The Account Takeover Kill Chain: A Five Step Analysis - ReliaQuest
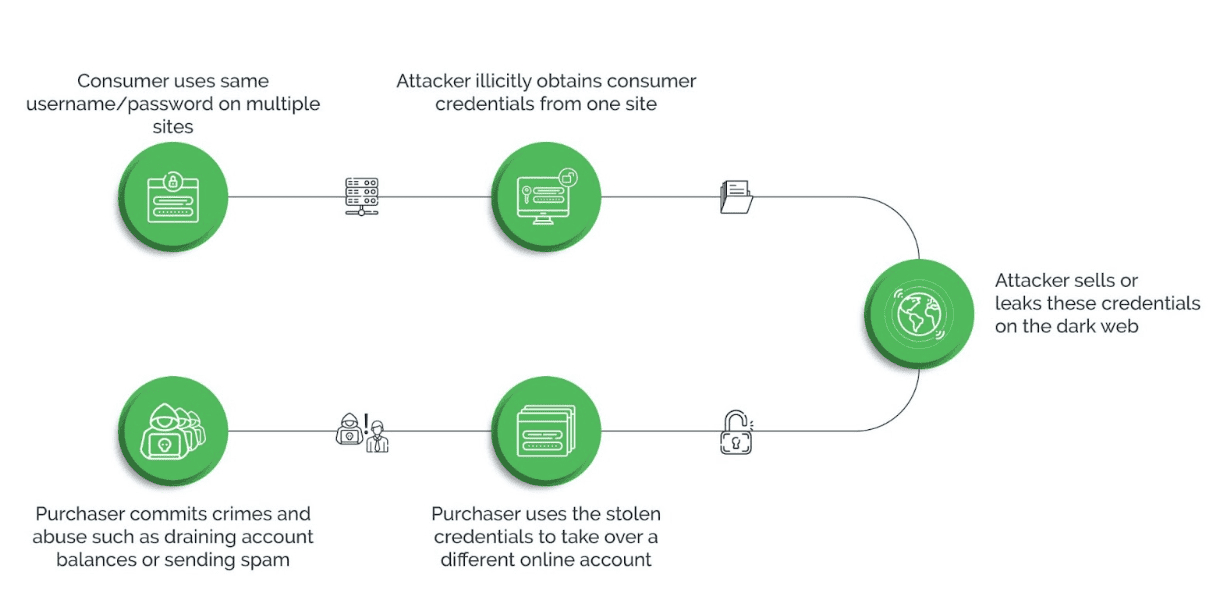
What Is Credential Stuffing?
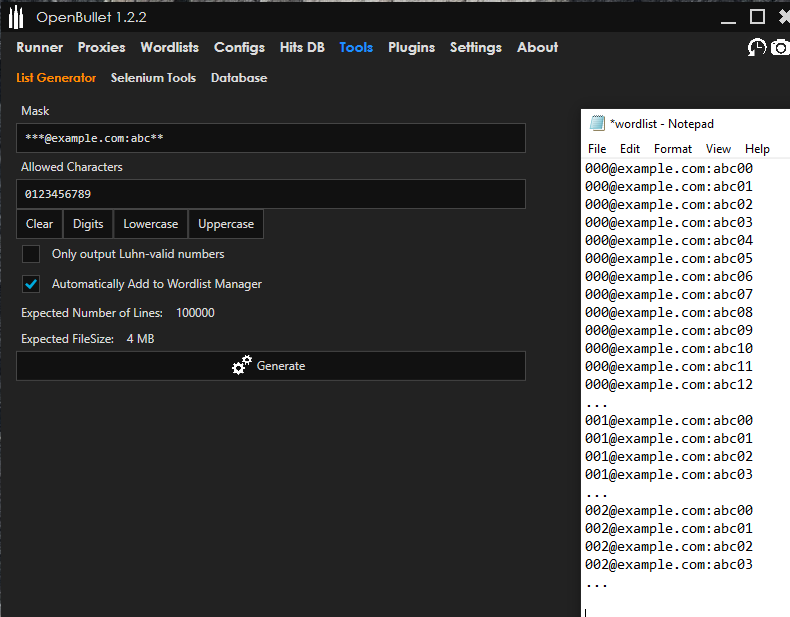
How Cybercriminals Abuse OpenBullet for Credential Stuffing
Captcha Solver: Auto Recognition and Bypass
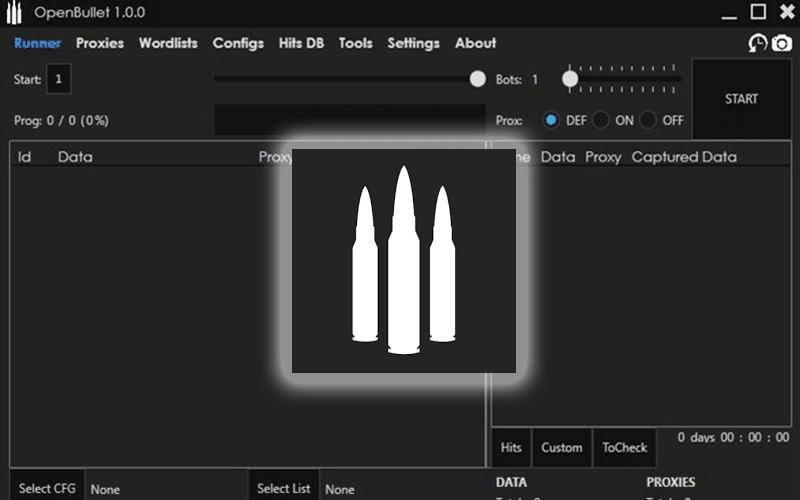
Cracking Tools that Automate Credential Stuffing & ATO
Credential Stuffing 2.0: The Use of Proxies, CAPTCHA Bypassing , CloudFlare Security, and GUI Tools
de
por adulto (o preço varia de acordo com o tamanho do grupo)